Here are the best privacy and security tools we’ve come across.
Most of them, we have talked about on our podcast. Some, we haven’t.
These resources help you to:
Let’s get started:
Tools to check your exposure
These sites help you understand how private you are when online.
Have I Been Pwned — Has Your Data Been Stolen?

Has someone hacked your personal information?
This handy website tells you whether your email address has been compromised in a data breach. When websites are hacked or data is stolen, you can verify if your details were exposed.
Simply enter your email address(es) and find out whether your details have been hacked.
We first talked about HIBP in episode 34 (at 1h 7m 17s)
BrowserLeaks — What is Your Computer Giving Away?

What is your computer giving away when you browse? Find out what any webpage you visit can discover about you. From your IP address (and possible location) through to your
We first talked about BrowserLeaks in episode 37 (at 29m 11s)
CheckUsernames — Where is Your Username Being Used Online?

This one is a useful tool to see where your username is being used on 160 different websites.
It might help you uncover some old profiles you may have set up, which may be publishing personal information you might not want publicly accessible.
We first talked about CheckUsernames in episode 42 (at 1h 6m 59s)
Tools to Stay Safe Online
Here, we’ve listed a range of ways to strengthen your online security. From privacy-friendly search engines through to a better browser, secure internet access, backup tools and password safety — these tools will improve your privacy and reduce your risk of becoming a target.
Choose a Privacy-friendly Search Engine

Everything you search for is captured, stored and tracked.
We all trust Google with the most intimate questions we’re too afraid to ask other people.
If you use Google regularly, you’re almost certainly sharing your location, insecurities, health status and more.
…and that’s terrifying.
Search engines use your search data to understand who you are, build a profile, and make money from you — all at the expense of your privacy.
Did I mention they’re sharing this with governments all around the world as well?
It’s time to put a stop to that.
Change your search engine to a safer, more private alternative.
Are these all safer? Yes. Are these completely secure? No. Nothing is.
Alternatives to Google Search
We first covered DuckDuckDuckGo in Episode 17 (at 1h 11m 8s), and Startpage in Episode 30 (at 19m 33s)
Switch to a Better, Safer Browser

If you’re using Chrome, you aren’t safe.
Why? Google tracks you everywhere when you use Chrome. Can you really trust a company who makes money from your personal data to use your browsing history for good? Absolutely not.
Brave Browser changes everything.
Using the same underlying code as Chrome, Brave ditches the nasty stuff and builds in ad-blocking and privacy by default — so you’re no longer the product.
There is:
- a desktop version (faster than Chrome)
and - a mobile version (easier to use than Chrome)
…and it’s insanely easy to switch.
You can instantly import all of your bookmarks, passwords and browsing history from Chrome — so you won’t even notice you’ve switched.
Give it a go — and you won’t look back.
We first discussed the Brave Browser in episode 10 (at 47m 40s)
If you sign up for the Brave Browser using the above link, and use the browser for more than 30 days — The FOMO Show will receive a $5 donation. It’s a great way to support the podcast — without spending a cent.
Don’t Want to Switch Browser? Install These 3 Privacy Extensions:
We first mentioned these essential browser plug-ins in Episode 30, at 1h 10m 40s. They help you to block ads and unwanted trackers, as well as making sure your connections are secured over HTTPS.
uBlock Origin: A Next-Gen Ad Blocker

Hate YouTube ads? Despise banner advertising?
You need this extension.
It blocks pop-ups, ads and privacy-infringing trackers. Because it strips out the bloat, webpages load faster.
Privacy Badger: Halt Invisible Trackers

Built by the Electronic Freedom Foundation, this plugin stops invisible trackers.
When used alongside uBlock, you’ll be well protected online.
HTTPS Everywhere: Enforce Encrypted Browsing

Made by the same organisation as Privacy Badger, HTTPS everywhere makes sure your web requests use HTTPS encryption, for maximum security.
Two Factor Authentication

Imagine giving a thief your real password — and being confident they can’t easily log in to your account.
With 2FA, you add a second step to log in to your accounts, such as entering a code sent separately (the second factor). This means that without having access to your “second factor”, usually a separate app, it is almost impossible for the attacker to access your account.
Most major websites and services support Two Factor Authentication: from cryptocurrency exchanges to your email provider. These include Google, Facebook, Coinbase, Twitter and Dropbox. There’s a great website which lists sites that offer two factor authentication.
Log in to your most important and valuable online accounts, then head to your your Account Settings and enable 2FA where you can. Prioritise services handling money, email or other personal data.
What should I use as my second factor?
Using a dedicated authentication app is the easiest method of 2FA. We recommend Authy, as it’s the most complete app out there for two factor authentication.
We first mentioned Authy in Episode 40 at 45m 8s
If that’s not for you, Google have an Authenticator app for Android and iOS, which works well — although if you switch phones, you cannot transfer your authenticator codes, but have to regenerate them instead.
Want maximum security? Take a look at Yubikey, a physical USB security key. You need to plug it in to your machine and physically press a button to authenticate login requests.
Manage your passwords securely with a password manager
If you do nothing else, do this.

Probably the biggest threat to your digital life is a malicious actor ending up with your username and password.
For most people, this would mean that they can take those details and use them on all sorts of other websites, because most use the same username/password combo.
With password managers like Lastpass, you’ll be able to sleep a lot easier, because they make having different passwords for every website a breeze. You do this through a few easy steps:
- Sign up for a free Lastpass account and make sure you use a unique, complicated password that you write down somewhere safe (on paper). This will be the only password you’ll need to remember from now on.
- Get the Lastpass plugin for your browser and login.
- Start accessing your favourite websites. As you access them, save the details in Lastpass (it should give you a popup each time).
- Change any duplicate passwords by generating new ones with the Lastpass ‘Generate Password’ feature.
- Use the same feature when you sign up for any new accounts.
- Enable 2FA with Authy so you can keep your password vault extra secure.
Lastpass will save any generated passwords, so you can make them as long as you want (we recommend 30 characters at a minimum). Eventually, you’ll get to the point where you have a unique password for each website – meaning that you no longer need to worry about knock-on effects from data breaches.
Password managers are the easiest way to reduce your identity risk profile and make yourself more secure online. Just don’t forget that master password! Check out some of the other features too – we find that the secure notes feature in particular is really useful.
Patching: Rewire Your Habits

“An update is available, install now?”
Notification fatigue is a trap. Clicking “no” opens you up to weaknesses which viruses and malware can exploit. Change your habits to protect yourself against recently-discovered vulnerabilities, improve the software you’re using and stay safe.
Actions:
- Make sure your operating system is up-to-date
and check that automatic updates are enabled - Open your frequently-used software, and check for updates
within your programs, this is usually under the “Help” menu. On mobile devices, check within your App Store app
Anti-Malware: Get Malwarebytes for Complete Peace of Mind
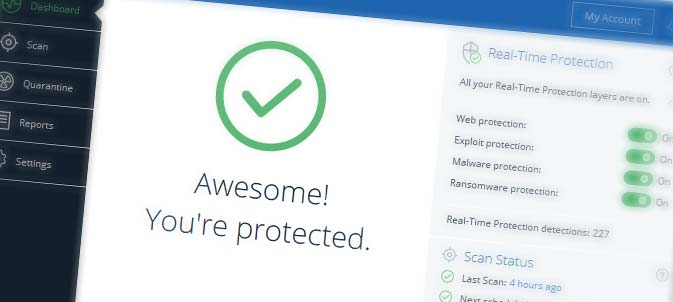
Anti-malware software protects you against evolving security threats: viruses, malware, adware, spyware, trojans, keyloggers and rootkits.
When it comes to real-time protection, we (along with millions of others) use and trust Malwarebytes.
For cryptocurrency enthusiasts, this is especially important. For real-time protection against the latest threats, it is a paid product — there’s a free 14 day trial, after which it will revert to the (great) free version, but without real-time protection against threats. We pay for the premium version — and recommend you do too.
We first covered Malwarebytes in Episode 13 at 41m 49s
VPN: Secure, Online Anonymity & Privacy to Mask Your Digital Identity

A VPN is an encrypted tunnel to the internet which masks your location and IP address (your unique identifier) when you use the internet.
Without a VPN (Virtual Private Network), you’re sharing your IP address with the sites you visit — as well as sharing your browsing habits with your internet provider.
Benefits of using a VPN:
- Securely encrypt your browsing activity — encrypt your internet browsing data up to the 256-bit Advanced Encryption Standard (AES), protecting your data from prying eyes.
- Bypass internet censorship and blocking — when your government or internet provider blocks certain websites, a VPN can get around these restrictions.
- Browse from anywhere in the world — make it appear as though you’re browsing from Germany, Switzerland, France or America. This means you can bypass region blocking (e.g. with Netflix or YouTube).
- Protect yourself against internet logging — make it hard for attackers or nation-states to see what you’re doing online.
A VPN can be installed on your desktop, laptop or mobile devices — so you can stay private wherever you are.
The main catch is that you’ll need to pay for a VPN service, as your internet activity runs through their servers. The good news, is that they’re cheap — from as little as $4 USD/mo, which is less than 14 cents per day.
We recommend these two VPN providers:
These two VPN providers are the ones we use and trust. They both have strict “no logging” policies — and accept Bitcoin as payment.
Recommended by Joe
Recommended by Matt
Warning against free VPN services: do not use free VPN services. They limit your internet speed, often monitor your browsing activity and sometimes even sell your data. It is not worth taking the risk.
Back up your data — and thank yourself later

If your computer is corrupted, stolen, destroyed or hacked — how can you get your data back?
Backups save your data — so you can restore to a point in time. They sound annoying, but you can set and forget with good processes in place. We recommend backing up to the cloud, so you can access your data from anywhere.
End-to-end encrypted online backup
End-to-end encryption means only you can access your files — and someone who tries accessing your files without your key can only see meaningless garbage. This is great for ultimate privacy.
| Product | Based in | Pricing from | Accepts Bitcoin? |
| pCloud Premium | Switzerland | ~$5 USD/mo | ✔️ |
| Tresorit Premium | Switzerland | ~$10 USD/mo | ❌ |
| Mega Pro Lite | New Zealand | ~$5 USD/mo | ✔️ |
| Sync Personal | Canada | ~$50 USD/yr | ✔️ |
| SpiderOak One | United States | ~$6 USD/mo | ❌ |
Are you technical? You can set up your own encrypted end-to-end backup for FREE using NextCloud. It’s open-source and self-hosted. You would need to take responsibility for keeping it (and your operating system) updated.
Cheaper backup services — with less privacy
If you want quick and easy backups, but don’t require or expect privacy, these are the best options:
Tools to Secure Your Identity
Your digital data is like gold.
Lots of companies pay a whole lot of money to get access to it – from your social media accounts to email addresses. In the same way that you’d secure any big amount of gold you held, you should similarly value your digital identity. Here are some ways that you can do that.
Security awareness – painfully obvious stuff you might be ignoring
You can get all the great programs in the world, but research consistently shows that your biggest risk factor is the person behind the keyboard – you. While we could write a list thousands of words long, here are some easy ways to stop putting yourself at risk:
- Don’t use your real name unless legally required to.
- It saves your data getting into the wrong hands. If you’re asked for personal information, get in the habit of giving out fake details.
- The only time you should put in your personal information is when you are making a delivery or interacting with your bank or government.
- Get a shredder. If you want to throw out a document containing personal information, shred it first.
- Check the address of any link before you click on it, particularly if it’s in an email (and especially without anti-malware)
- Avoid downloading from questionable sources – e.g. unusual torrent links, or little-known programs/executables
- Be really careful about what you install. Do you really need to install an application you’re only going to use once (and may forget to update?)
- In addition, uninstall programs you no longer use
- Only input a password if you’re certain you’re on the correct website (a password manager can help with this)
- Set different passwords for each website you use
- Get a temporary email address (see below)
Lock down your social media privacy settings
When you use social media, you’re giving out your personal information.
If you need to use social media, make sure your default privacy settings are locked down tight.
Here are links for the privacy settings pages for:
Make sure you:
- Limit what unknown people can see about you
- Switch off location sharing
- Stop your name from appearing in search
- Stop your mobile number or email being used to find you
- Disable ad targeting & personalisation
- Block automatic facial recognition
- Prevent posts from automatically being “public”
Using Firefox? Quarantine Facebook & Google. If you’re using Firefox, there are two extensions that can section off Facebook and Google from your other internet browsing — so they can’t follow you around the web. Get Facebook Container and Google Container for Mozilla Firefox.
Email security
Maildrop: Instant email addresses for short-term use
Ever wanted to download to a “free” file, but had to fill out a form to get it?
Maildrop to the rescue.

If you need to give out an email address for something unimportant, use an email address ending with @maildrop.cc — you can then access the inbox directly from the Maildrop site, without signing in.
For example, you can immediately access the inbox for test@maildrop.cc, or any other email address at their website.
Maildrop is designed to be quick and easy — but all email addresses are publicly accessible, so bear that in mind before using it.
An alternative is SharkLasers, which gives you a random email address to use temporarily, but it’s not as quick or as simple as Maildrop.
33mail: Generate unique email addresses easily
It happens so much. You make a new email address, sign up for a few websites and all of a sudden you’re getting bombarded by marketing from companies you’ve never heard of. You don’t know who’s shared your data, with who or to what extent.

33mail is a great way to counteract this. It lets you have a different email address for each website, all of which will forward to a ‘master’ inbox you choose. Even better, you can create these unique emails at the time you sign up, making the process easy and painless.
Compared to Maildrop, 33mail is more permanent and private, letting you generate new addresses that will forward to your regular email address.
You’ll get access to free disposable email addresses that you can delete at any time — so you can take control of spam and keep your inbox clean.
Get notified if your data is leaked with Firefox Monitor
Wouldn’t it be great if you had a way to know if your online details have been compromised?
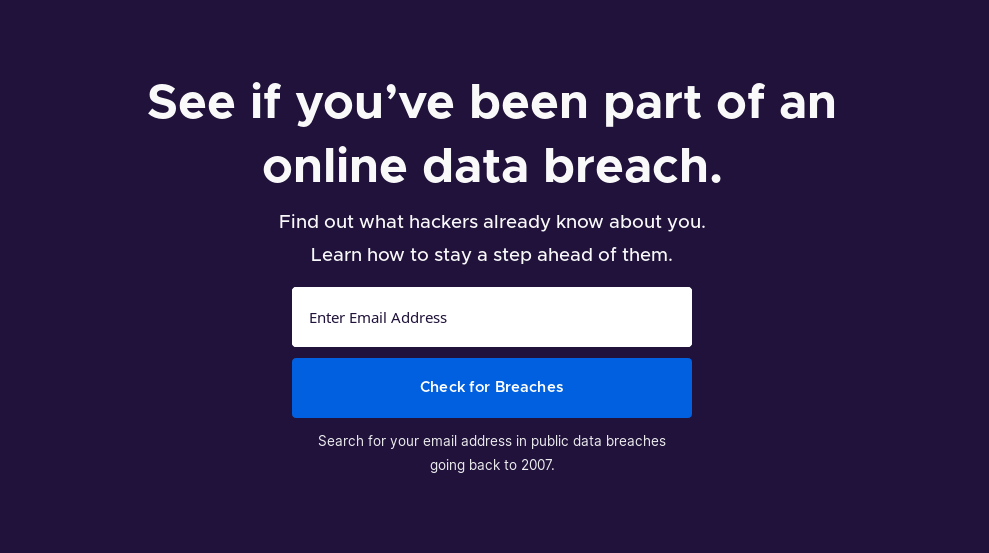
Luckily, Firefox have a great solution to this, with Firefox Monitor notifying you if your details are leaked online. This means that you can get quick notifications if your identity is at risk, and take some steps to reduce the risk.
Send Large Files Securely With Firefox Send
Like it or not, most cloud storage providers are snooping on everything you upload – particularly the big ones like Google Drive and Microsoft Onedrive. Not only are they looking through all your data, there’s increasing evidence that a number of government employees have full access, too.
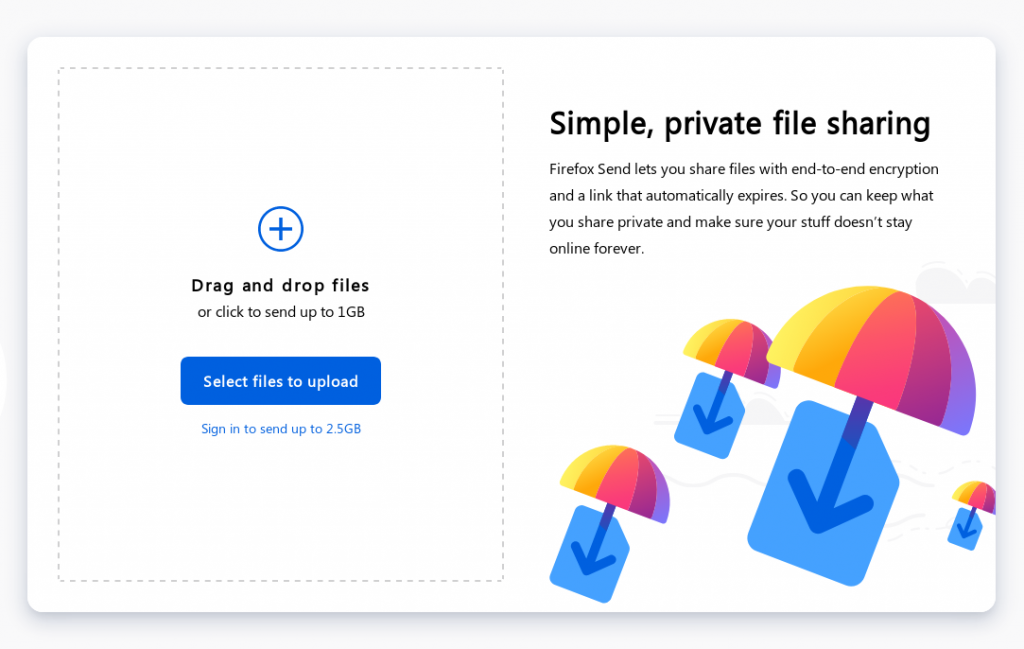
Firefox Send is a great answer to this. It lets you upload and share fully-encrypted files without having to worry about some balding 50-something bureaucrat scrolling through your family photos while sipping his morning coffee.
You don’t need to sign in for small files, and you can set download and time limits for the sharing of your files.
Have a tool you want to suggest? Spotted an issue? Drop us an email at fomoshow@protonmail.com
Bonus: Level Up Your OS with Linux
Real talk – Windows isn’t actually very good. The world’s most popular operating system costs money to use, has questionable security, breaks things when it updates and just generally gets in your way. It’s slow, prone to viruses and sends a whole bunch of data back to Microsoft about your system use.
You may have sat there looking at your latest blue screen of death or having to restart your computer again after installing updates and wondered if there was a better way. And you’d be right!
Linux is an open-source operating system developed by a huge community of programmers, software engineers and tinkerers. It’s been around for more than 20 years and runs most of the server and cloud architecture in the world. This means its solid, reliable and built to be secure – and almost everything that runs on Windows also runs on Linux.
For 15 years or so, Linux was predominantly the realm of software engineers and uber-geeks. Most of the good stuff was tucked away behind command lines and documentation – user experience came a distant second to functionality. However that’s changed rapidly in the last few years – Linux distributions like PopOS, Elementary and Manjaro have made the user experience incredibly easy – to the point where it is genuinely better than Windows for the average user at almost everything.

We won’t go into too much detail here (as we’ll probably write a bigger guide later), but switching to Linux will mean that you’ll not only be using a more stable, secure system by default which is entirely controlled by you, but once you get used to it, you’ll probably find you’ll be far happier with your desktop experience.
The best way to see if you like the Linux experience? Download an ISO and boot it up in Virtualbox or directly from USB (just search online for a guide).




